Wenn ich mehr Zeit hätte, oder vielmehr sie nicht mit anderen Dingen verplempern würde, kämen hier möglicherweise öfter Rants wie der folgende, aber vielleicht ist es auch besser, dass das nicht der Fall ist.
Teil 1: Welcome to the internet
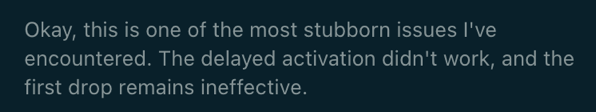
Die Deutsche Bahn hat in den letzten Jahren ihre Website und ihre Apps durchaus verbessert. An manchen Stellen blitzt aber noch immer die alte Zeit durch. Da wird für Verbindungen folgende Meldung ausgegeben.
Abgesehen davon, dass ich mit der Formulierung »zur Stabilisierung des Zugbetriebs« nicht viel anfangen kann, wird hier für die detaillierten Informationen auf eine andere Website mitsamt URL verwiesen, diese aber nicht verlinkt. Da wäre sogar der Klassiker »Mehr Informationen finden Sie hier« besser gewesen.
Teil 2: Design by Excel?
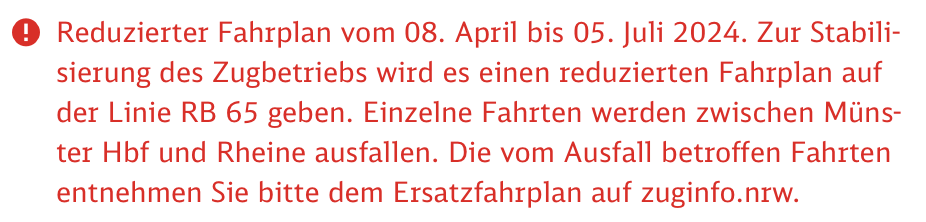
Nachdem ich die nicht verlinkte URL selbstständig aufgerufen habe (ein Hoch auf PopClip), muss ich danach die erwarteten Details selbst suchen, weil auf der Seite sämtliche NRW betreffende Meldungen aufgelistet werden. Vermutlich wäre bei einem konkreten Deeplink zum korrekten PDF die Problematik der Nicht-Verlinkung noch stärker aufgefallen. Es muss also die Suche bemüht werden, um die Meldungen zur spezifischen Bahn zu finden, gesagt, getan. In der Meldung, muss ich den Text erstmal einblenden, der mir jedoch keine neuen oder gar detaillierte Informationen liefert. Ich werde darauf hingewiesen, dass letztere im Ersatzfahrplan zu finden sind, der natürlich ein PDF ist, aber immerhin als Link. Das »Schönste« (und der eigentliche Auslöser für dieses Rant-Posting) kommt aber erst noch. In diesem PDF finden sich Tabellen, in denen die ausfallenden Fahrten markiert sind.
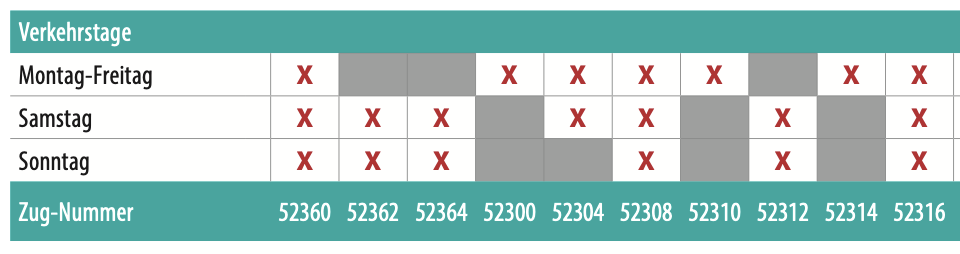
Wow, da muss aber offenbar viel »stabilisiert werden«. Ich bin kurz davor, eine andere Zugverbindung zu wählen. Doch ob der schieren Menge der augenscheinlich ausfallenden Fahrten werde ich skeptisch.

Ich konsultiere also die Legende zu dieser auf den ersten Blick sehr eindeutig erscheinenden Tabelle und siehe da, irgendjemand bei der Eurobahn hatte die grandiose Idee, stattfindende Fahrten mit einem roten X zu markieren – entgegen jedweder Konvention. An dieser Stelle würde ich gern die Formulierung »kannste dir nicht ausdenken« verwenden, aber ganz offensichtlich stimmt das ja nicht. Da ich meine übliche Phrase nicht verwenden kann, fehlen mir erstmal die Worte.
(Pause)
Irgendjemand hat sich das ausgedacht, und irgendjemand anders hat es vermutlich noch geprüft und für passend befunden. Diese Menschen sind offenbar nicht viel im Internet unterwegs.
Ich bin kein Freund der Bezeichnung »best practices«, aber gewisse Konventionen haben sich doch »eingebürgert«, und ein rotes X in einer Tabelle steht in aller Regel nicht für Positives, sondern meist für etwas fehlendes in einem Vergleich – eine haarsträubende Wahl. Die einzige These, die mir dazu in den Kopf kommt, ist, dass das Layout ursprünglich mit den diesbezüglich begrenzten Mitteln einer Tabellenkalkulation erstellt wurde und dann … tja, dann war vielleicht jemand am unpassenden Tag krank und Deadline und wichtig und ZACK ist es auf der Webseite, bzw. im PDF.
¯\(ツ)/¯
Edit: Fehler korrigiert